- Rogers Community Forums
- Forums
- Internet, Rogers Xfinity TV, & Home Phone
- Internet
- Hitron Router Man in the Middle Attack?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Subscribe
- Mute
- Printer Friendly Page
Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
11-04-2018 05:37 PM
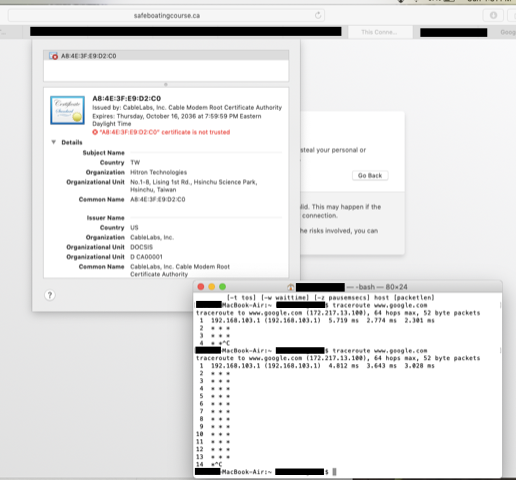
My wife went to the https://safeboatingcourse/ca site a couple of times. The second time, she got a TLS cert warning:
Certificate is not trusted. Issued by: CableLabs Inc. Cable Modem Root Certificate Authority
Organization: Hitron Technologies
Organizational Unit: No. 1-8, Lising 1st Rd, Hsinchu Science Park, Hainchu, Taiwan
It looks very much like the modem is acting as a man-in the-middle to an https protected site.
To add complexity to this I found:
- I had inadvertently left the Guest network running for a week
- my wife's laptop was connected to the Guest network
- her laptop was routing to a different gateway IP (found via first hop in traceroute)
- our modem had taken additional IPs that I was not aware of:
- The gateway I had configured: 192.168.174.1
- The additional gateways that the modem "camped out upon" seem to be: 192.168.100.1, 192.168.101.1, 192.168.102.1, 192.168.103.1
Superficially, I would think "I left the Guest network on, got compromised". But I find it strange that the cert being used is a cert provided by the modem and that the modem has multiple (hidden) gateways.
My questions are:
- has anyone heard of this attack?
- Could this be anything other than an attack? Does the Hitron Modem have multiple gateways? Does it use a different gateway for the Guest network?
- suggested course of action
Re: Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
11-04-2018 09:10 PM
Hello, @bityz.
Welcome to the Rogers Community Forums! 🙂
Thank you for an interesting post. I'm assuming the domain extension of the website address your wife was trying is "dot ca" not "forward slash ca". It's possible the browser was not able to reach the resource if "forward slash ca" was being used and resulted in the certificate error.
We haven't heard this certificate error on our forums so far.
Community - please chime in and share your expertise on this matter.
Cheers,
RogersMoin
Re: Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
11-05-2018 06:52 AM
Sorry for the typo. Yes. I meant dot ca. See attached (redacted) screen grab (sorry for poor resolution)
Re: Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
11-05-2018 08:09 AM
Re: Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
05-04-2020 09:05 AM
Wow I just ran into this same issue. I installed a replacement Hitron modem from Rogers just this morning and afterwords I received a certificate warning from outlook.office365.com from the same CA (CableLabs Inc. Cable Modem Root Certificate Authority) from outlook connecting to my work email. Thankfully I know enough to click "no" but I know alot of people would not be. This is not cool Rogers.
Re: Hitron Router Man in the Middle Attack?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Content
05-05-2020 09:04 AM
Greetings Community!
I think the best course of action here would be to send an email with these findings to abuse@rogers.com.
That is normally the place for customers to report and forward any concerns regarding the abuse of Rogers network.
Regards,
RogersCorey